Responding effectively to the the challenges of NIS security requires inter alia the exchange of information on risks and incidents. Accordingly, the NIS Directive requires OESs and DSPs to report incidents with a significant/substantial impact. A key deliverable of the NIS Directive is also the creation of a computer security incident response teams network (‘CSIRTs network’) in order to contribute to the development of trust and confidence between Member States and to promote swift and effective operational cooperation. In that regard, Member States are required to designate one or more CSIRTs responsible for risk and incident handling. While national CSIRTs are primarily tasked with operational assistance, they may also be the competent recipient for the mandatory incident reports by OESs and DSPS.
Irrespective from the mandatory incident reporting, entities may want to share information about incidents and threats to warn others and also to seek support in responding to these incidents and threats. The Luxembourgish CSIRT CIRCL, for instance, gathers, reviews, reports and responds to computer security threats and incidents. In order to share threat indicators and intelligence within private and public sectors, CIRCL operates several MISP instances for different types of constituents. The MISP threat sharing platform is a free and open source software facilitating such information sharing while also storing and correlating indicators of compromises. Information is shared on a platform of trust between trusted partners. Contributors to a MISP instance can decide with whom they want to share their information: only within their organisation,within a set community, within connected communities or with all communities. Users of MISP benefit from the collaborative knowledge about existing malware or threats. the aim of this trusted platform is to help improving counter-measures used against targeted attacks and set-up preventive actions and detection. The MISP project, developed inter alia by CIRCL, includes multiple sub-projects to support the operational requirements of analysts and improve the overall quality of information shared. MISP provides certain default attributes and categories to classify an incident/threat.
Along with the core format, MISP taxonomies provide a set of already defined classifications replicating for instance CSIRTs/CERTs classifications or national classifications. The fixed taxonomies provide a practical method to tag efficiently events and attributes within a set of MISP instances where taxonomies can be easily customised to meet the local requirements of an organization or a specific sharing community. When using MISP, the MISP taxonomies are available and can be freely used based on the community practises. To date, the MISP project provides a ‘NIS Cybersecurity Incident Taxonomy‘ based on the Commission Recommendation (EU) 2017/1584 of 13 September 2017 on coordinated response to large-scale cybersecurity incidents and crises.
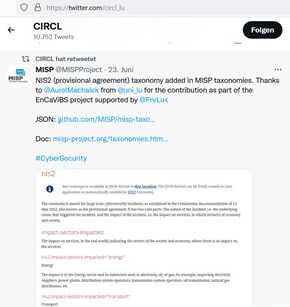
As part of the EnCaViBS project and in light of the forthcoming NIS 2.0 Directive, the EnCaViBS team developed a new ‘NIS2 proposal taxonomy‘ allowing the identification of essential and important entities as defined under the Proposal for a NIS 2.0 Directive. The taxonomy will be updated once the final Directive is published.
Further information: